If we’re to pinpoint a combat with out an finish or a particular winner, that will be the combat between cybersecurity consultants and cybercriminals.
This can be a unending problem.
As know-how advances, criminals who search to take advantage of vulnerabilities have gotten extra artistic. On the opposite aspect, organizations have gotten extra cautious – and able to staying forward of the ever-changing digital threats.
With out a proactive strategy, a single assault could cause your small business to halt its operations – and even trigger its failure. We’re speaking a few fortune in fines, enterprise income, and authorized charges, to not point out the mark this could go away on a model’s status.
The dangers right now are large, extra quite a few, and extra versatile than ever. To guard your small business and keep forward, you want a proactive strategy to cybersecurity and a strong resilience technique.
On this submit, we’ll train you why this issues and how one can obtain it.
Understanding digital threats
A ransomware assault takes place each 40 seconds right now.
On common, cybercriminals create 1.4 million web sites for phishing monthly, most of which comprise pages that mimic an actual firm – reminiscent of yours.
So, we’re taking a look at round 2,200 estimated cyber assaults each single day! What does this inform us?
This goes to point out that digital threats are right here, and they’re extra quite a few and profitable than ever. Immediately, when most companies want know-how to progress and succeed out there, cybercrime is among the greatest threats to their success.
The implications of a digital assault can differ from minor to devastating for a enterprise. If you’re hacked, your organization’s info and that of your prospects can find yourself within the flawed fingers.
You may get into authorized hassle and pay authorized charges that may price billions! To not point out, relying on the assault and its success, this could flip a really profitable enterprise into ash.
It additionally is dependent upon the kind of assault, in fact. Some assaults are way more harmful and dear than others.
Ransomware assaults, as an example, are very frequent these days, and these criminals have reached even the most important manufacturers on the market.
EXAMPLE: In July 2020, GTW World, an enormous US journey companies firm, made an unlimited ransom cost – $4.5 million in Bitcoin to Ragnar Locker, a cybercrime ransomware group. The assault took down 30,000 computer systems and compromised tons of knowledge, together with safety documentation, monetary data, and staff’ private knowledge.
One factor is for sure: cyberattacks know no bounds, and each firm can fall prey to at least one, or many. Nevertheless, in case you have an ingrained coverage and take a proactive anti-fraud strategy, you may mitigate lots of the dangers and may have a backup plan to fall on if issues go flawed.
What’s the commonest type of digital assault utilized by hackers right now?
The risk panorama is shifting as know-how progresses.
The threats you fought just some years again are extra versatile and superior now, and new threats are gaining energy with each passing minute.
Supply: Sprintzeal
With that in thoughts, listed below are the most typical kinds of safety threats right now:
1. AI-powered assaults
Effectively, criminals certain love the advances in synthetic intelligence (AI).
They use it greater than ever. In accordance with a report by Sapio Analysis and Deep Intuition, the rise in assaults within the final couple of years is usually led by means of AI, with 85% of attackers utilizing generative AI.
Nearly all of assaults lately are facilitated by bots and different merchandise of synthetic intelligence. Cybercriminals use AI to automate every little thing from phishing to produce chain assaults.
2. Ransomware assaults
Ransomware assaults lately are extra focused and, subsequently, extra damaging. Attackers now encrypt knowledge and demand cost to maintain it non-public.
A few of the ransomware assaults are so well-planned and executed, that they price companies thousands and thousands. NotPetya, the greatest ransomware assault to this point, made a financial influence of $10 billion and impacted main corporations.
3. Provide chain assaults
When cyber criminals goal your organization’s provide chain, they’re performing a provide chain assault. If they’re profitable, they will fully infiltrate your community, and also you received’t even discover it till it’s too late.
On this case, criminals infiltrate trusted distributors and use them to compromise the software program and attain the tip customers. The potential injury has no limits.
4. Phishing assaults
Phishing has been round for a very long time, and it stays one of many important methods criminals take over web sites. On this case, the hacker will ship a misleading message disguised as an e-mail from an actual entity, requesting that the recipient reveal their login particulars.
In different phrases, they will fake it’s your firm sending a message to a buyer or an worker, demanding their login particulars or cost info. With the information readily available, they will use it to log in and do their injury.
In accordance with Statista, 76% of companies have reported being a sufferer of such an assault in 2022 alone.
Supply: Statista
5. DDoS assaults and SQL injections
Distributed denial of service (DDoS) assaults happen when criminals use a number of gadgets to hit a server with faux visitors. The consequence? The web site turns into inaccessible and can’t perform usually. The assault paralyzes a server by overloading it and, in lots of instances, makes a web site go offline.
This may be devastating for giant companies with plenty of visitors since they lose through the downtime. There have been experiences of main e-commerce platforms struggling such downtimes, even within the busiest durations.
Equally, SQL injections enable hackers to entry your knowledge and shut it down. They inject SQL instructions into present scripts, and after they succeed, they will execute quite a lot of instructions – together with shutting it down altogether.
Supply: Spiceworks
6. Malware assaults
Malware assaults have been round for the longest time, however they continue to be probably the most frequent cyberattacks on the huge internet. Malware is malicious software program or virus designed to one way or the other hurt your computer systems, servers, networks, or purchasers.
In reality, any sort of malicious software program that serves the aim of harming or exploiting a programmable community or machine falls beneath the “malware” class.
Digital threats: stop, detect, and mitigate future assaults
Whereas digital threats now come hooked up to using know-how and the web, and eliminating them altogether is not possible, there are some measures you may take to forestall, detect, and mitigate them.
Extra particularly, you want what we name a cyber resilience technique – and right here is tips on how to create it.
Safe your knowledge – and carry out knowledge backups
The rule of thumb in cyber safety is to forestall it when doable. It’s at all times higher and cheaper to forestall a risk than it’s to repair the injury.
So, begin by securing your knowledge.
In case your knowledge isn’t as safe as it may be, that is the right time to go for a safer choice. Begin by transferring knowledge and assets to a safer infrastructure or a special software program i.e., carry out a system migration. Simply make sure you optimize the system migration course of and maintain it as protected as doable.
Subsequent, it’s time to again up all the information. That is a part of your restoration plan – you could have one other location for the necessary info in case it will get misplaced, or your small business falls sufferer to a cyber assault.
Knowledge backup is common work – not a one-time measure. Repeatedly again up techniques and significant knowledge utilizing quite a lot of options reminiscent of exterior arduous disks and cloud-based software program.
Defend your self from authorized hassle
Knowledge safety legal guidelines change each day.
They regulate thousands and thousands of companies with a purpose to shield prospects. In case of an information breach or some other cyber assault, it’s essential to make it possible for your small business is compliant with present rules to keep away from hefty authorized charges and issues.
Whereas there are many methods to stick to the altering knowledge privateness legal guidelines’ necessities, some practices are extra standard than others, reminiscent of using the banner cookie.
Cookie banners are a solution to meet the necessities unobtrusively. They seem as a pop-up when individuals go to your web site, informing them about using cookies and asking them for consent.
When the customer accepts the cookies and the storage and use of their knowledge, you might be legally coated. It’s nonetheless your duty to guard that knowledge but when a breach happens and also you’ve taken the mandatory measures to forestall it, you at the very least received’t have to consider authorized penalties.
Have a digital assault response and restoration plan in place
Backing up knowledge is simply step one among your restoration plan. In lots of instances, it received’t matter in case you have the information saved some other place whether it is already compromised.
So, how will you create an incident response plan?
An incident response plan consists of a number of components:
- Preparation: Doing no matter doable to forestall any incident from occurring
- Incident detection: Discovering out what the issue is
- Incident containment: Ensuring that the injury doesn’t get larger
- Restoration: Mitigating the state of affairs to the perfect of your skill
Merely put, a cyber incident response plan is a doc, a plan that outlines what your organization would do within the occasion of a safety incident reminiscent of an information breach.
Most of the cyber assaults are unavoidable, even in case you have a wonderful safety system in place. Nevertheless, such a plan gives you one thing to work on – an motion plan, should you’d like.
The response plan may have pointers in your group to take earlier than an incident happens. Then, it’ll comprise steps that it must take to establish when the techniques or knowledge are compromised.
Subsequent, it gives you concepts on how one can mitigate the injury if and when it happens. And eventually, it gives you a plan on tips on how to get better from several types of cyber assaults. 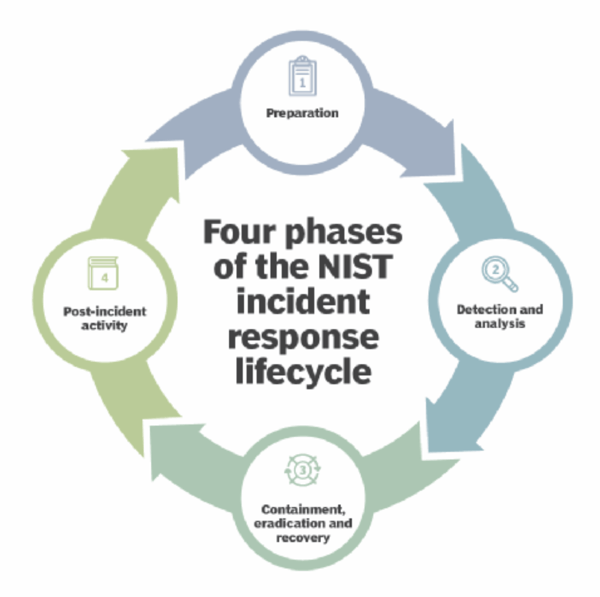
Supply: TechTarget
Conduct steady monitoring
Cyber threats are greatest handled once you catch them in actual time. Nevertheless, with so many threats and makes an attempt, it’s not possible to maintain observe of every little thing – and see each little glitch that signifies an assault.
Companies and cybersecurity professionals have a fantastic set of instruments at their disposal for real-time risk detection. Many of the threats are avoidable should you catch them earlier than they penetrate your safety system, and instruments like internet proxies and bot detection may also help you do that continuous, with none human effort.
You’ll be able to check and consider your digital presence and knowledge by utilizing monitoring and evaluation instruments and companies. These will robotically conduct vulnerability assessments, penetration testing, and safety audits to handle any vulnerabilities in your small business’s digital merchandise, reminiscent of a web site or an app.
Carry out worker coaching
Do you know that 88% of knowledge breach incidents are brought on by an worker who made a mistake?
Except you prepare your staff and train them tips on how to combat off digital threats, your small business is at hurt. It doesn’t matter how nice of a software program you’ve invested in to trace and mitigate assaults or how thorough your restoration plan is – a single worker can go away the digital door open for hackers, typically unintentionally.
Because of this, right now, greater than ever, it is very important educate your workers on frequent digital threats, tips on how to establish them, and the way to reply to them. Consider your staff as the primary line of protection you could have towards cyber criminals. It’s your duty to coach them on the subject to forestall hackers from utilizing your staff to hurt the enterprise.
Encryption and knowledge safety
Whereas accumulating and utilizing person knowledge is roofed with consent, it’s nonetheless your duty to encrypt that knowledge and maintain it protected. Methods like encryption defend delicate info towards cyber assaults and brute drive assaults like ransomware and malware.
Merely put, you’d be translating all delicate knowledge into code or one other type in order that solely the individuals who can learn it will likely be capable of entry it.
Common evaluations and updates
Cyber resilience is a piece in progress.
You’ll be able to’t merely create an incident response or restoration plan, spend money on some software program options, and overlook concerning the matter.
Criminals are extra artistic with each passing day, which implies that the methods you employ right now would possibly not work tomorrow. With that in thoughts, you must commonly overview and replace your technique to align with new digital threats and the business’s greatest practices.
The advantages of a robust cyber resilience technique
Whenever you take measures to detect, stop, and mitigate cyber threats, you might be forming your cyber resilience technique. Listed below are among the the explanation why that is necessary:
Enhanced safety
A very good technique protects your group towards digital threats. It consists of every little thing from backing up the information, addressing vulnerabilities, and making ready for any potential cyber assaults.
Aggressive edge
Though digital threats are extra quite a few than ever – and way more harmful than earlier than, most companies function on the premise that they’re too small for cybercriminals to focus on them or that their outdated methods labored to date, so why wouldn’t they now?
Which means that most of your competitors may have outdated or poor cyber resilience methods in place – if any. In accordance with an UpCity ballot, 50% of companies don’t have a cybersecurity plan in any respect.
This provides you a wonderful aggressive benefit. For starters, you might be much less more likely to grow to be a sufferer of a cyber assault. However you can even present the target market that you’re devoted to sturdy practices and place your self as a extra dependable, reliable accomplice.
Stronger status
A robust cyber resilience program safeguards the status of your small business. Should you do that repeatedly, it’ll foster belief amongst your prospects, in addition to your companions and stakeholders.
A stronger status in a aggressive market is every little thing. It equals extra prospects, stronger partnerships, and, in fact, extra earnings.
Compliance with rules and legal guidelines
As we talked about, legislation compliance is essential with regards to knowledge safety and privateness, and should you fail to stay compliant, you’re looking not solely at knowledge leaks and hacks however at penalties and authorized issues, too.
Your cyber resilience program needs to be targeted on business rules and requirements above every little thing else to make sure that, at any given second and in any situation, your small business is compliant with the present legal guidelines.
The price of being non-compliant is sort of thrice larger than the price of being compliant lately. On common, the price of compliance is $5.47 million in comparison with $14.82 million for non-compliance.
Supply: Fortra
Enterprise continuity
Whereas not all cyber assaults are avoidable, a very good safety plan and techniques may also help you keep away from most of them. For any digital risk you efficiently stop or mitigate, you might be making certain enterprise continuity and success.
Let’s say that you just handle to guard your small business from a ransomware assault that will in any other case price you thousands and thousands – or break it altogether. You simply helped your small business survive. Let’s say you prevented limitless phishing assaults or malware attempting to get to your knowledge. Congratulations, you’ve efficiently safeguarded your monetary stability and your status.
Should you stop a DDoS assault or an SQL injection, you may preserve a seamless workflow and stop main losses.
Future-proofing your cyber resilience plan
Immediately, not taking your small business on-line is an enormous drawback. In reality, normally, companies should go browsing to achieve their focused viewers and make gross sales. Nevertheless, with this benefit come many dangers, most of them within the type of digital threats.
Digital threats are in all places – and it’s your duty to guard your small business. It’s your job to create a fierce cyber safety resilience technique, implement it, and maintain it consistently up to date.
Digital threats evolve and alter extra continuously than anybody can comply with. That being mentioned, it’s your job to maintain up with the modifications in cybercrime in addition to cybersecurity methods. To be one step forward, you undoubtedly wish to think about predictive developments and imminent dangers, particularly with the rising reputation of AI and distant work.
Synthetic intelligence and machine studying give cybercriminals a plethora of choices with regards to focusing on companies.
Irrespective of how large or small your organization is, the danger is at all times current. Don’t assume, “there’s no manner they’ll hassle hacking my enterprise.” That is what a lot of the corporations that fell sufferer to digital assaults thought previously!
Get a cybersecurity deep dive with Dr. Chase Cunningham as he talks about Zero Belief.

